Fuente: Chron – Autor: Dwight Silverman
“There are a different set of security concerns because of who these people are,” said Caleb Barlow, vice president of threat intelligence at IBM Security.
Modern CEOs use email and search the web — rare is the chief executive that has an assistant print out emails these days — and so they are just as likely to run into malicious websites and phishing emails, Barlow said. And with CEOs at bigger companies, they are likely to be older and not immersed in digital culture.
“There is a generational gap there,” he said. “These people didn’t grow up with computers. They know M&A, finance and corporate management because they came up learning these issues. But that’s not always true with cybersecurity.”
Barlow said there are three types of cyberthreats CEOs and other C-suite executives face.
Phishing attacks. Phishing involves sending an email that appears to come from a trusted source in an attempt to get the recipient to take some action. They may contain a link to a malicious website, or request personal or proprietary information, or may try to get the recipient to take some other type of imprudent action. Highly specific phishing emails, aimed at high-value targets, are known as “spear phishing,” and a target as big as a CEO is considered “whale.”
“CEOs meet a lot of people,” Barlow said. “A CEO might get an email that says, ‘Hey, I met you at the XYZ conference, remember we talked about how your wife and mine both went to Stanford? I’ve been meaning to talk to you about a deal.’ It’s easy to figure out what a CEO is into, and get this kind of information about them.”
Business email compromise. Known by the acronym BEC, this involves a hacker getting into a company’s email system, then using that access to spoof the CEO and order employees to perform some action. A 2017 FBI report indicated that this type of cybercrime is among the most rapidly growing, with a 1,300 percent increase in complaints and more than $3 billion in losses.
“The bad guy sends an email, it looks like it came from the CEO, and it says, ‘Hey, I am working on a deal, please keep this confidential, and I need you to wire $2 million from this account to another account,’” Barlow said. “This has resulted in some of the largest losses we’ve seen.”
Doxxing. This is the practice of digging up detailed personal information about a person and making it public. Because CEOs of larger companies have been in the corporate and public spotlight for a while, a lot is known about them. That makes them a target for doxxing, which can be used to gain leverage on a CEO.
“You can find out things like where their children go to school, you might post health records, or anything that could cause problems for a CEO,” Barlow said.
The best way to prevent these from happening to a CEO is a coordinated training effort not just for the chief executive, but also for the people around him, Barlow said. The CEO needs training similar to what all employees get, but it also needs to be coordinated with training for the people around him.
For example, the direct reports to the CEO need to know that “I am never going to ask you by email to wire money someplace,” he said. That’s true of other C-suite executives and those who report to them.
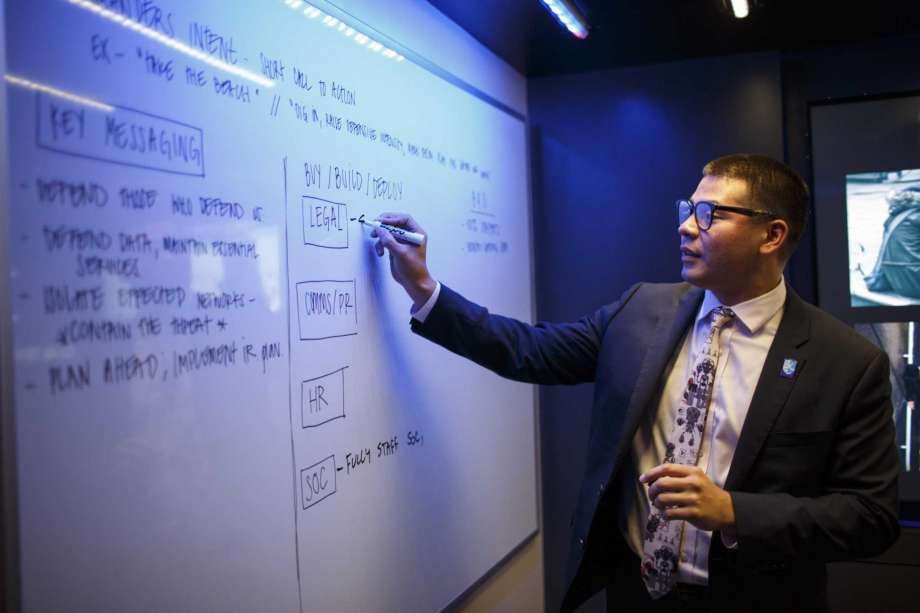
As part of its cybersecurity training products, IBM has built a mobile security command center that is aimed at teaching executives how to respond to a breach at their companies. It’s similar to the mobile command operations set up by the military or police, complete with an 18-wheeler loaded up with computers and wall-sized screens.
“CEOs are used to making decisions slowly and deliberately, with lots of research and information available to them,” Barlow said. “This teaches them what it’s like to make important decisions in real-time when they are on the right side of a security breach.”
dwight.silverman@chron.com
twitter.com/dsilverman